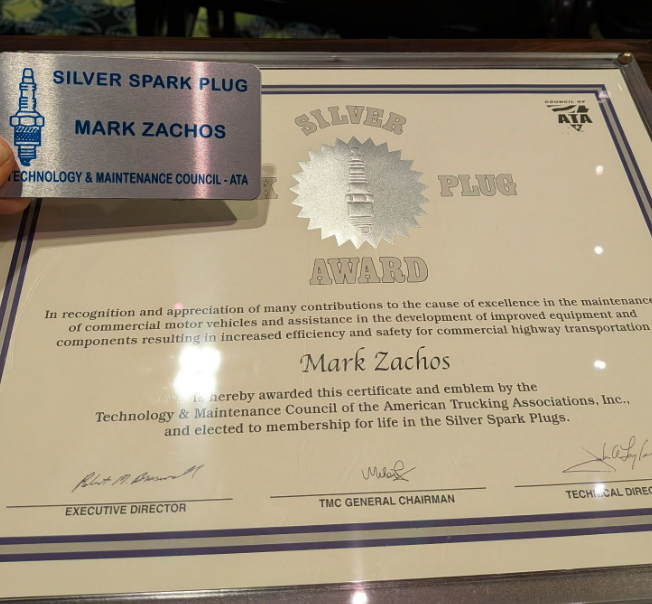
The following cybersecurity column by Mark Zachos, president and founder of DG Technologies, recently appeared in the Winter 2026 issue of Fleet Maintenance & Technology, the quarterly magazine published by the American Trucking Associations (ATA) Technology & Maintenance Council (TMC). Zachos also chairs the TMC Cyber Security Task Force.
The Role of AI in Cybersecurity in 2026
By Mark Zachos
Looking at cybersecurity predictions for the upcoming year, you’d be hard-pressed to find a list that does not predominantly involve artificial intelligence (AI).
AI is engrained into much of what we do online – allowing access to even more immediate information and compressing once-complex and time-intensive tasks into those that can be accomplished with just a few lines of instruction and the simple push of a button. In trucking, AI together with telematics can help fleets run more smoothly, more safely and more cost-effectively.
Fleet management technology has evolved dramatically, becoming smarter and more practical for day-to-day operations. Telematics systems monitor everything from a truck’s exact position to how hard the brakes are being pushed, how much fuel is being burned on each trip and even when a driver is idling too long. The constant stream of real-time information gives managers a clear picture of performance, highlighting where efficiency can be improved.
An efficient and effective productivity tool, AI builds on all of that data by transforming it into useful guidance, like recognizing trends in driver behavior, flagging early signs of mechanical issues before they cause breakdowns and forecasting when a vehicle will need maintenance. AI can also recommend optimized delivery routes by taking into account construction zones, road closures and weather.
Almost daily, we’re learning new ways for AI to enhance and streamline industry. However, at the same time, AI is also productive for cyber criminals because it allows them to more easily create exploits, or attacks, that then go out and phish for information. Further, it can create ways to attack equipment by helping guess passwords or by helping attackers better understand the actual bits and bytes of CAN JBUS messages to decode them.
But while attackers have an advantage with AI as a tool, on the other side, we “good guys” also have an advantage in using it to help bolster our defenses against cyberattacks.
Steven Piper, a certified information systems security professional (CISSP), believes that, at least for now, AI will still continue to give IT security teams the advantage.
“I don’t know if threat actors are ever going to have the upper hand with AI,” Piper said in November as part of a webinar on his “Top 5 Security Predictions for 2026” for the International Information System Security Certification Consortium (ISC2).
Head of marketing and research firm CyberEdge Group in Fort Lauderdale, Fla., and cybersecurity online news source Security Buzz, Piper included in his predictions an uptick in high-profile attacks involving deepfake photos, audio and video, and agentic AI becoming “a game-changer for information security teams over the next three years.”
Unlike AI, which simply makes recommendations or analyzes data, agentic AI uses machine learning models to take action on its own to achieve a goal – deciding what steps to take, carrying them out, then adjusting behavior as conditions change.
In trucking, this might look like AI autonomously adjusting delivery routes without human assistance to avoid storms or road closures, or re-planning delivery schedules and automatically contacting customers when a driver is delayed. It also could look like automatically scheduling repairs, ordering parts and booking repair shop appointments when AI detects early signs of engine trouble.
Like AI in recent years, agentic AI also opens the door to more cyberattacks and raises the stakes for trucking and other industries due to its capacity to make cyberattacks more automated, more adaptive and more persistent.
In place of a human initiating an attack, agentic AI acts on its own, mining for weaknesses, adjusting tactics as needed and carrying out other parts of attacks without supervision, making human threat actors even faster, stealthier and more efficient. For sectors as interconnected as trucking, that means cybersecurity should be viewed as just as essential as maintenance or route planning.
With new capabilities like agentic AI transforming the security landscape, both defenders and adversaries now have unprecedented power. But one constant remains – people continue to be the greatest vulnerability, and the greatest asset, in any security program.
Most cyber incidents don’t start with a sophisticated hack, but with human error. Someone clicks a convincing link, reuses a weak password or rushes through a process that should have been double-checked.
Some simple, impactful security measures organizations can take include requiring employees use long passwords and multi-factor authentication, using phishing simulation software to train staff to pause before clicking on questionable links and to encrypt files containing sensitive information and data.
Organizations also can implement role-based security, authorizing employees at different levels to perform different operations, for instance, having controls around who is authorized to change passwords, or which employees have access to certain data and decryption keys for encrypted data. Human risk management reduces everyday vulnerabilities by building habits, awareness and systems that help people in an organization make safer choices.
Technology is only going to keep advancing and, with that, threats will keep intensifying. The individual organizations that succeed in 2026 will be the ones that align their strategies, their tools and, most importantly, their people.
For further information:
Dearborn Group, Inc.
33604 West Eight Mile Road
Farmington Hills, MI 48335
1 (248) 888-2000
sales@dgtech.com
General Contact:
John McNelis
Sales and Marketing Manager
jmcnelis@dgtech.com
Visit our website: www.dgtech.com
Our Services Portal: https://www.truck-connect.com/
Follow us!
X: x.com/DGTechnologies
Facebook: facebook.com/vehiclenetworksolutions
Instagram: Instagram.com/dg_technologies/
YouTube: www.youtube.com/@DGTechnologies

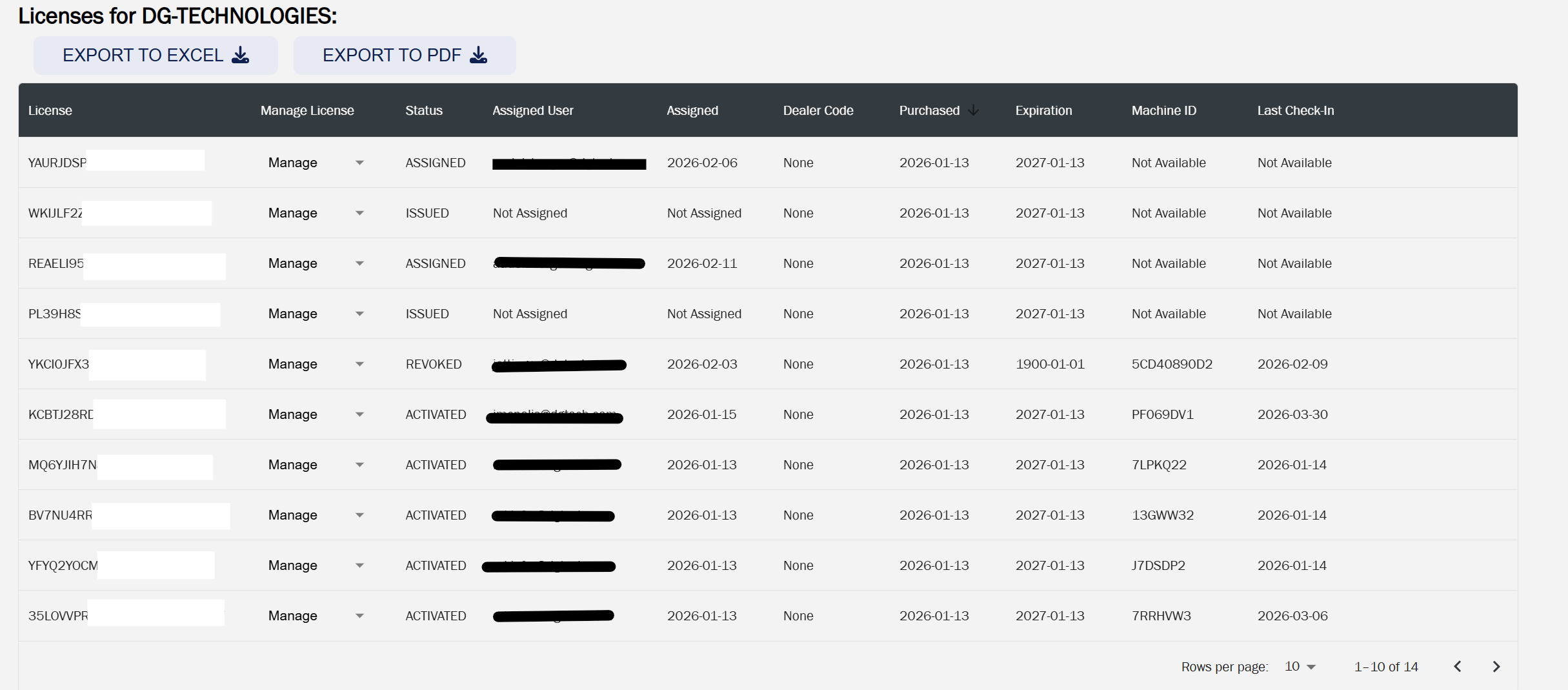
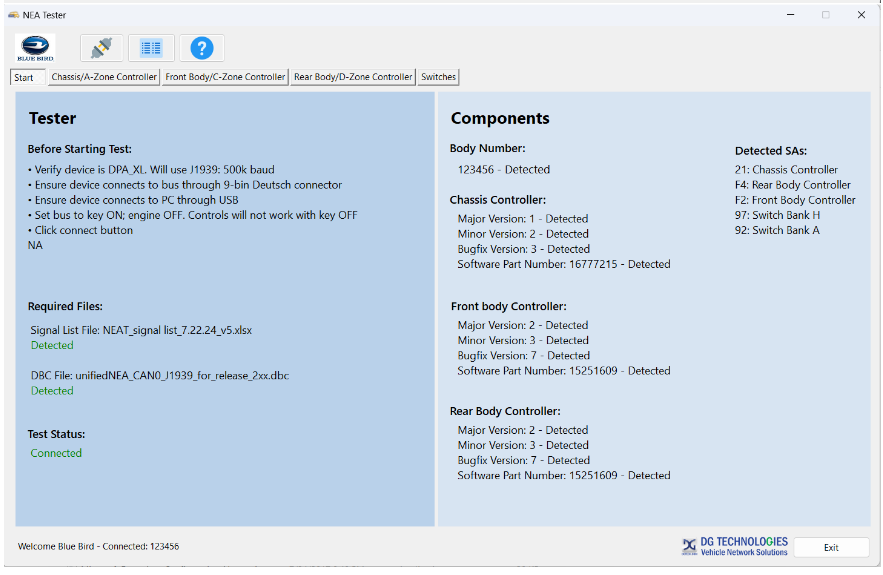
 DG Technologies’ NEAT Software for Blue Bird Buses: Available Now!
DG Technologies’ NEAT Software for Blue Bird Buses: Available Now!